When most law firms think “cyberattack,” they imagine a bad afternoon. A suspicious email. A few locked files. A hinderance. In reality, a serious cyber incident is not a technical inconvenience.
It’s a major law firm interruption event.
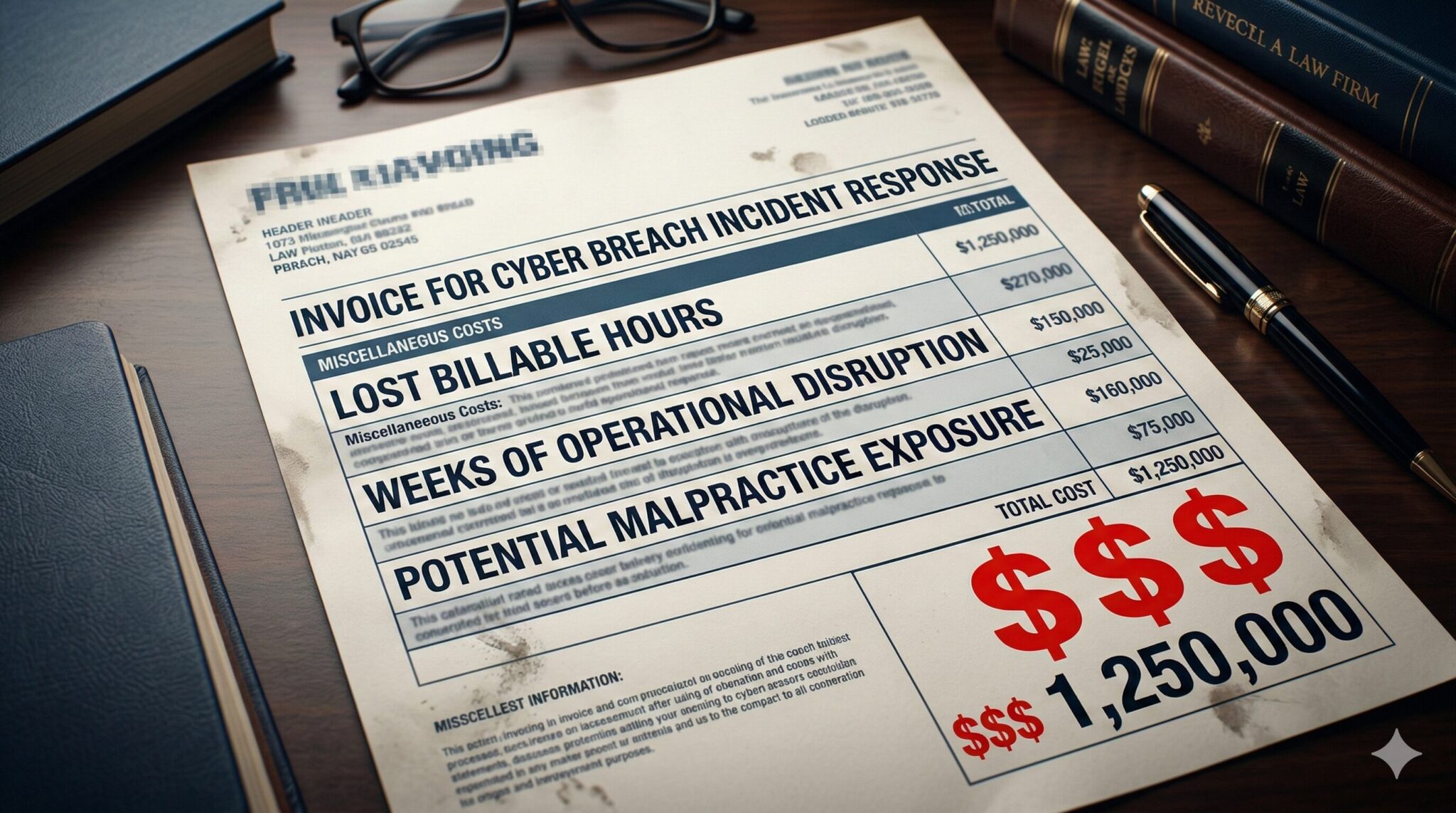
For Illinois law firms — especially in the Chicago market — a breach can mean:
- Weeks of operational disruption
- Lost billable time
- Forensic investigations
- Insurance coordination
- Client notification discussions
- Regulatory review under Illinois law
- Potential malpractice exposure
Cybersecurity in law isn’t just about protecting servers.
It’s about protecting billable hours, client trust, and professional reputation. That’s why CTI Technology specializes in data protection and compliance for law firms in Chicago. We’ve been providing IT services for law firms for over 20 years.
What Actually Happens During a Law Firm Breach
A breach rarely begins with ransomware flashing across the screen.
It usually unfolds quietly.
Stage 1: Silent Exposure
According to IBM’s Cost of a Data Breach Report, the average time to identify a breach is approximately 200+ days, with additional time required for containment. That means attackers often sit inside environments for months before discovery.
During that time:
- Email accounts may be monitored
- Credentials harvested
- Client files accessed
- Backup systems evaluated
- Privileged accounts mapped
There’s no alarm.
No obvious outage.
Just quiet access.
This is rarely a firewall problem.
It’s a detection maturity problem.
Stage 2: Discovery & Containment
IBM’s reporting has consistently shown that once a breach is identified, containment can take an additional two months on average, pushing total breach lifecycles toward nine months in many cases. The same research shows that organizations that test incident response plans regularly reduce overall breach costs compared to those that do not.
An incident response plan does not prevent a breach.
It prevents chaos.
Recovery Time — Where Law Firms Really Feel It
Detection and containment are only part of the story.
Recovery is where law firms feel the financial impact most directly.
Industry ransomware recovery reporting, including TotalAssure’s Average Ransomware Recovery Time statistics for professional and law-related industries, has shown recovery timelines averaging around three weeks (approximately 20–22 days) in many cases.
Twenty-two days. Even when core systems are technically restored sooner, the operational tail lingers:
- Rebuilding work in progress
- Reconstructing time entries
- Reviewing client files for integrity
- Managing client communications
- Fulfilling reporting obligations
- Coordinating with insurers and forensic teams
Each day saved is billable time preserved.
For example, a mid-sized Illinois firm with 12 attorneys billing $350/hour that loses just 3 full days of productivity is looking at:
12 × $350 × 8 hours × 3 days = $100,800 in disrupted billable capacity.
That’s before regulatory costs, forensic expenses, or insurance deductibles.
Law Firms Remain a Target
Law firms continue to be targeted specifically due to the sensitivity of client data.
The FBI’s Internet Crime Complaint Center (IC3) has issued alerts noting law firms are attractive targets for credential theft, ransomware, and business email compromise. Additionally, Verizon’s Data Breach Investigations Report continues to show that credential abuse and phishing remain among the top initial access vectors across industries, including professional services.
Illinois-Specific Obligations Law Firms Must Consider
For Illinois law firms, a breach is not just technical. It triggers regulatory and ethical responsibilities.
Under the Illinois Personal Information Protection Act (815 ILCS 530):
- Breach notification must occur without unreasonable delay
- If more than 500 Illinois residents are affected, notice to the Illinois Attorney General is required
For attorneys, this intersects directly with:
- Illinois Rules of Professional Conduct 1.6 (confidentiality)
- ABA Formal Opinion 483 (client notification guidance in breach situations)
Cyber insurers increasingly require safeguards such as:
- Multi-factor authentication
- Backup validation
- Documented incident response plans
- Security awareness training
Failure to maintain reasonable safeguards can create not only regulatory exposure — but malpractice exposure. Cybersecurity maturity now directly affects insurability.
What a Proper Incident Response Process Looks Like for Illinois Law Firms
The firms that recover fastest are not necessarily the ones who avoid incidents entirely. They’re the ones who prepared deliberately. A defensible incident response process for an Illinois law firm should include:
- Defined detection and escalation procedures
- A named incident response team (IT, leadership, legal counsel, insurer contact)
- Clear isolation and containment steps
- Evidence preservation protocols
- A regulatory and client notification workflow
- Backup restoration validation steps
- A structured post-incident review process
To make this practical, we’ve created a simplified incident response workflow aligned with Illinois law and ISBA guidance.
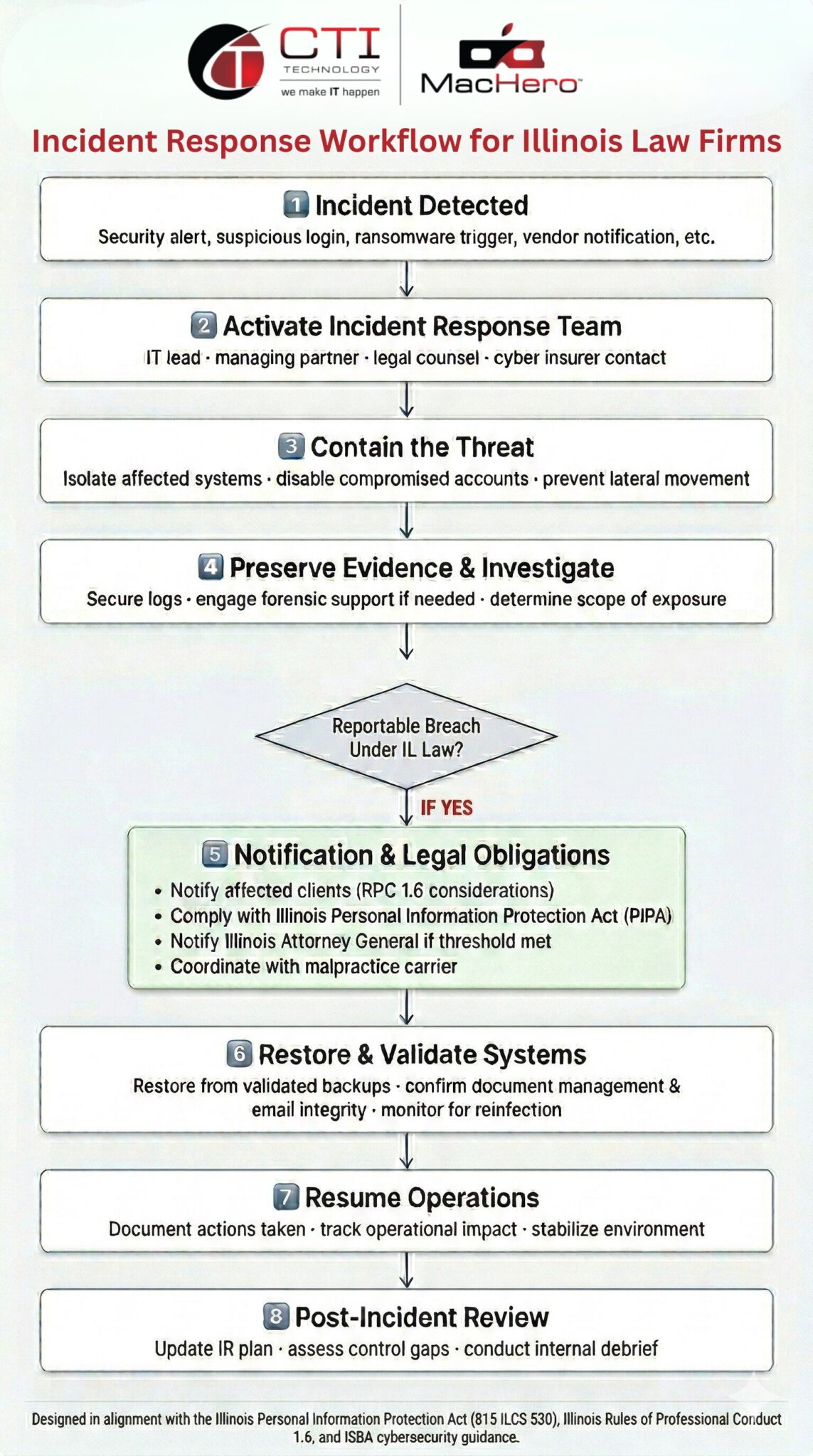
Download the Illinois Law Firm Incident Response Workflow here.
If you’re on the fence about working with an IT company, take a look at our guide to see if it’s the right choice: Does Your Chicago Law Firm Really Need an IT Company?
Why Is CTI Technology The Best Choice For IT Services In The Chicagoland Region?